How The Phone Of the Richest Man In The World Was Hacked
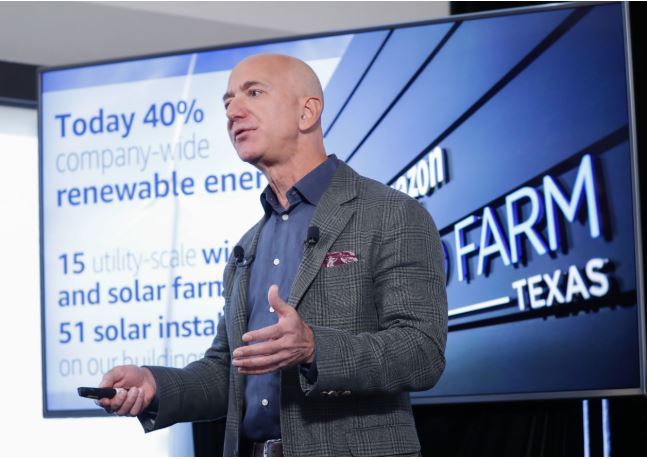
Posted by George on Fri 24th Jan, 2020 - tori.ngJeff Bezos
On the afternoon of May 1, 2018, Jeff Bezos received a message on WhatsApp from an account belonging to Saudi Arabia’s crown prince, Mohammed bin Salman.
The two men had previously communicated using WhatsApp, but Bezos, Amazon’s chief executive, had not expected a message that day — let alone one with a video of Saudi and Swedish flags with Arabic text.
The video, a file of more than 4.4 megabytes, was more than it appeared. Hidden in 14 bytes of that file was a separate bit of code that most likely implanted malware, malicious software, that gave attackers access to Bezos’ entire phone, including his photos and private communications.
Those details were part of a forensic analysis that Bezos had commissioned to discover who had hacked his phone, an iPhone X. He has been on a singular quest to find out who penetrated the device after he said The National Enquirer’s parent company threatened to release his private photographs and texts in early 2019. Those pictures and messages showed Bezos, who was married at the time, with another woman, Lauren Sanchez. The analysis did not connect the hack to The Enquirer.
The forensic report on Bezos’ phone was at the heart of a United Nations statement Wednesday raising concerns about the digital tactics of Crown Prince Mohammed. The analysis essentially accused the Saudi prince of using malware created by a private cybersecurity company to spy on and to intimidate Bezos, who also owns The Washington Post. The Post, which has published coverage critical of the Saudi government, had employed Jamal Khashoggi, a dissident Saudi writer who was killed in the Saudi consulate in Istanbul in late 2018.
The report’s conclusions renew questions about the shadowy world of private hackers for hire. For the right client, or the right sum, such hackers apparently infiltrated the phone of one of the world’s wealthiest and most powerful men.
The report did not say which private cybersecurity company was used, but suggested that the Tel Aviv-based NSO Group and Milan-based Hacking Team had the capabilities for such an attack.